Interpreting Identity Graph Data
The legend helps you understand and interpret the visual elements presented on the identity graph, helping you quickly gain context around the current state of a graph.
To display the legend, select the Legend button in the top right.
Node Types
There are three node types, each indicated by a different sized node displayed in the graph.
| Node | Description |
|---|---|
| Root node | Largest of the nodes and centered on an identity graph. This node represents the access object that the graph displays. All edges extend from this node. |
| Intermediate node | Nodes that are aggregates of access and do not explicitly represent any access. You can expand an intermediate node to show the direct nodes. |
| Direct node | Smallest of the nodes representing explicit access that is assigned to a user. When you expand an intermediate node, direct nodes are displayed. |
Access Objects
Colors and icons are used to distinguish between the following types of access objects:
| Access Object | Description |
|---|---|
| Identity | Human identities, application identities, and AI agents that have access. Note: Your organization must have Machine Identity Security and Agent Identity Security to view application identities and AI agents in the graph. |
| Accounts | Human accounts and machine accounts. Note: Your organization must have Machine Identity Security to view machine accounts in the graph. |
| Role | Represented by a green circle. Roles are the grouped sets of access assigned to an identity. |
| Access Profile | Represented by a pink circle. Access profiles are bundles of entitlements assigned to an identity. |
| Nested Entitlement | Represented by a grey circle. |
| Assigned Entitlement | Represented by a blue circle. |
| DAS Application | Represented by a white circle. An application in Data Access Security is an on-premise or SaaS platform that requires identity security functions to manage access to accounts on them. Note: Your organization must have Data Access Security to view applications in the graph. |
| DAS Resource | Identity Graph displays top-level resources from Data Access Security. Top-level resources are the highest-level organizational container that often include business resources. These resources represent the root folders for the configured application. Notes:
|
| Group | A set of access objects have been grouped by a predefined or custom grouping. |
Access Object Counts
When an identity is selected in Identity Graph, the graph displays the nodes and number of access objects that were directly assigned to the identity. By default, this number excludes access objects that were assigned through roles or access profiles. Identity Security Cloud counts all access items assigned through roles and access profiles when it calculates the number of items assigned to an identity. As such, this number may differ in Identity Graph and Identity Security Cloud.
The number of access objects an identity is assigned in Identity Graph may change once users add filters to the data.
Entitlement Hierarchy and Inheritance
The graph visualizes data available in Identity Security Cloud, pulling together an identity's access and displaying the relationships between access objects.
When viewing the graph in the top-down layout:
-
If you have opened the graph for an identity, the relationship between access objects is displayed from the identity down to the entitlement.
-
If you have opened the graph from an entitlement, moving from top to bottom in the entitlement hierarchy, it displays from the parent to a top-level entitlement and then down to a child entitlement. The entitlement hierarchy can have multiple layers, the highest level having no further parents and the lowest level having no further children.
Note
An entitlement’s assignment and relationship to other entitlements determines the color of its node.
Assigned Entitlements
Blue nodes represent assigned entitlements. These entitlements are directly associated with an identity or assigned via an access profile or role connected to the identity.
Note
Child entitlements of an assigned entitlement are not shown from an identity view, as the permissions of those child entitlements are not relevant to the assigned entitlement of the identity.
Nested Entitlements
Grey nodes represent nested entitlements. These entitlements are not directly assigned to the identity, but instead they are the upstream of an entitlement that is assigned to the identity. Nested entitlements may have multiple levels with parent and child entitlements.
Nested entitlements are displayed to show the inheritance path and the relationships between entitlements, showing what an entitlement can inherit from, and what entitlements can be inherited from it.
You can view identities that have inherited access to an entitlement by right-clicking the node of a nested entitlement and selecting Load indirect access. Identities that have indirectly received access to this entitlement are displayed. You can export this data by opening the Data Table and selecting Download CSV. This data can also be exported through the JSON Export Tools.
Data Access Security Objects
Data Access Security Admins and Org Admins can view applications and top-level resources from Data Access Security in the graph. You can use the visualizations to determine whether an identity has access to sensitive data and how that access may have been assigned to the identity.
Identity Graph consumes data classifications from Data Access Security to display resource nodes that indicate the sensitivity of the data included in the resources.
You can select the Data Access filter from the Filters menu to view the subgraph for data access pathways. You can also use filter criteria to filter the graph for access pathways that contain that specific sensitive data category.
To view further information about an application or resource in Data Access Security, right-click the node and select Open in DAS. Data Access Security opens in a new tab with details about the object.
Outer Rings on a Node
Outer rings appear around an access object when an action is performed on that node.
| Outer Rings | Description |
|---|---|
| Object is locked | A purple ring is present around a node that is locked. After repositioning a node, you can lock it in place to prevent it from moving when you manipulate other nodes on the graph. You can lock multiple nodes in place and manipulate the surrounding unlocked nodes. This feature is useful in dynamic layout. |
| Object is selected | A white ring is present around a node when it has been selected. Select one or more access objects to highlight the node and perform actions. |
| Object is right-clicked | A blue ring is present around a node when right-clicked. Right-click an object to select an action to apply to the node. |
Comparison Mode
When comparing the access for two identities, the access object’s nodes display in different colors to indicate which identity has access to that specific item.
| Comparison Option | Description |
|---|---|
| Primary only | The objects that only the primary identity has access to are denoted by blue rings. |
| Comparison only | The objects that only the second identity has access to are denoted by orange rings. |
| In both | The objects that both identities have access to are denoted by green rings. |
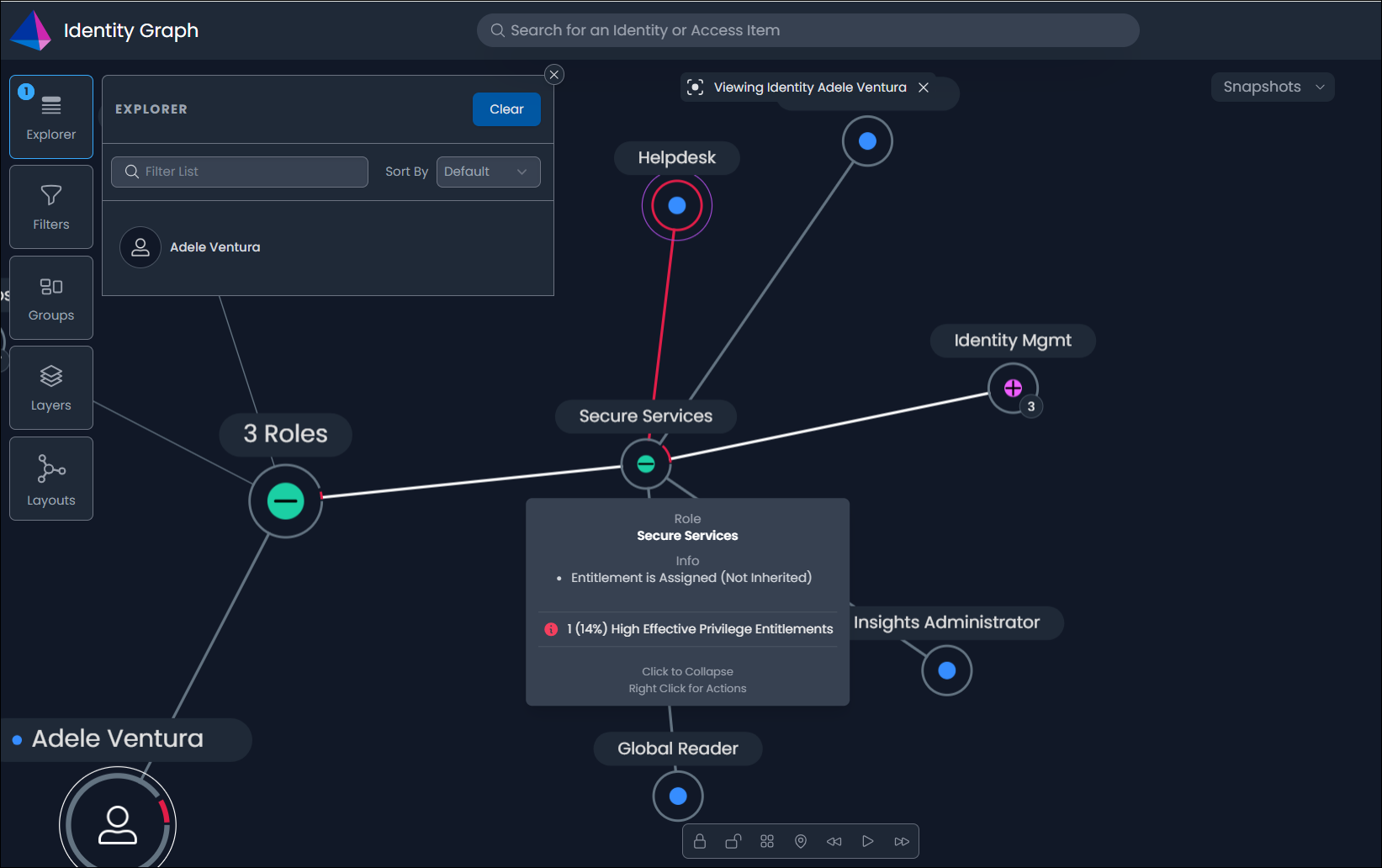
Ring Indicators
The ring indicators on a node indicate the composition of privileged entitlements within that access object. These objects may include multiple privileged entitlements with varying privilege levels (high, medium, or low). Privilege levels are represented by specific colors, which are defined in the graph’s legend.
In this example, a portion of the ring indicator around the Secure Services node is red to indicate that the role includes the Helpdesk entitlement, which has a high privilege level.
Hovering over the Secure Services node displays further information about the role, including the percentage of its entitlements that have a high privilege level. You can use the percentage to assess the level of risk associated with the access object.
Note
For more information on privileged access, refer to the Privilege Classification documentation.
Lines
Lines represent the connections and relationships between access objects.
Select a line between two nodes to gain information on requested access. When you hover over an edge for requested access, a small text box displays information including who made the access request, when they made it, and who approved it.
| Line | Description |
| Path | A link between two nodes that represent an existing relationship. |
| Outlier rare access | An entitlement that is assigned to less than 1% of the organization. Identifying identities with access that is significantly different than their peers. Note: Your organization must utilize the Identity Outliers feature in Identity Security Cloud. |
| Multiple path | A multiple-path line is visible when the system grants access to an object from more than one access item, including:
|
| Granted last 30 days | Access to the entitlement was granted within the last 30 days. Identifying new and potentially unauthorized access. |
Documentation Feedback
Feedback is provided as an informational resource only and does not form part of SailPoint’s official product documentation. SailPoint does not warrant or make any guarantees about the feedback (including without limitation as to its accuracy, relevance, or reliability). All feedback is subject to the terms set forth at https://developer.sailpoint.com/discuss/tos.
 displays on the nodes of resources without assigned owners.
displays on the nodes of resources without assigned owners.