Processing Identity Data
When changes occur to identity data or access model configurations (identity profiles, roles, access profiles, or applications), corresponding access for your identities may also need to change. These changes happen through identity processing, which can be initiated in response to events, scheduled, or executed manually.
- Event-based processing immediately processes identity data for identities changed during an aggregation and for identities modified in provisioning actions.
- Scheduled processing occurs every morning and evening for identities that meet the requirements.
- Time-based processing uses an identity attribute to schedule the exact date and time an identity will be processed.
- Manual processing can be initiated following changes to configurations like role definitions or identity attribute mappings.
These actions were previously performed by the process known as an identity refresh.
Event-Based Processing
When an aggregation or provisioning process modifies an identity, that event initiates identity processing to automatically analyze the identity to make sure the rest of their data is accurate.
If the identity's data is out of sync with the configurations, it performs these changes:
- Updates identity attribute according to the identity profile mappings.
- Determines the identity’s correct manager through manager correlation.
- Updates the identity’s access according to their assigned lifecycle state.
- Updates the roles assigned to the identity based on the criteria they meet, and updates their access based on which roles were added to or removed from them. However, identity processing does not validate that access was successfully provisioned to the identity after starting the provisioning process.
Scheduled Processing
In some identity profiles, lifecycle states and other identity attributes are calculated through rules or transforms that determine values based on time, rather than on aggregated data.
Example
The lifecycle state attribute is commonly calculated with a transform that compares the current date to a hire date or termination date attribute.
Scheduled identity processing runs twice daily, at 8:00 AM and 8:00 PM in the tenant's configured time zone (default CST/CDT).
- At 8:00 AM:
- Active and Inactive (short-term) identities with an account on a source configured with attribute synchronization are processed.
- This operation performs all necessary actions for event-based processing for the specified identities. To optimize system performance, Identity Security Cloud updates identity attribute data and reevaluates user access data (roles and lifecycle-driven access) for only those identities with changes.
-
At 8:00 PM:
- If your site has any roles implemented, Active and Inactive (short-term) identities are automatically processed.
- If you have no roles defined, identities are processed based on their identity profile. If any of its identity attributes are marked as requiring a periodic refresh, Active and Inactive (short-term) identities are processed.
- This operation performs all necessary actions for event-based processing for the specified identities. To optimize system performance, Identity Security Cloud updates identity attribute data and reevaluates user access data (roles and lifecycle-driven access) for only those identities with changes.
Notes
- The scheduled processing jobs are queued for execution at the specified times. Other queued or in-progress operations may delay the job start.
- Times are based on your site's configured time zone (default CST/CDT).
Time-Based Processing
Time-based processing uses the nextProcessing identity attribute to determine the next date and time an identity should be processed. This identity attribute must be configured per identity profile.
Identities will be refreshed at the date and time set in this attribute, as well as during scheduled processing.
To configure time-based processing:
-
Go to Admin > Identity Management > Identity Profiles and select the identity profile you want to edit.
-
Select Mappings.
-
Map the Next Processing Date (
nextProcessing) attribute to an account attribute containing the date the identity should be processed next.Important
The
nextProcessingattribute is often mapped to a start date or an end date. This attribute can be assigned a transform so that the next processing date is calculated based on your business needs. For example, you can build a transform that represents the following logic, which will evaluate thestartDateandendDateattributes and select the earliest future date:if (startDate > now) return startDate + "T06:00:00" else if (endDate > now) return endDate + "T15:00:00" else return nullFor additional information on using transforms to set the next processing date, refer to the Developer Community.
-
Select Save to complete the mapping.
Best Practice
If you've used transforms in your mappings, SailPoint recommends previewing and verifying your identity profile changes before selecting Apply Changes.
The next time this source is aggregated, this value will be populated for identities and they will be processed as applicable at the assigned date and time.
The identity will undergo processing at that date and time, in addition to during scheduled processing.
Manual Processing
When you create or edit identity profiles, roles, or access profiles, you must manually initiate identity processing to update your identities. This is required to apply your access model updates to your identities and recalculate access requirements, even when the identities have not changed. You can also initiate identity processing for selected identities.
Manual Processing for All Identities
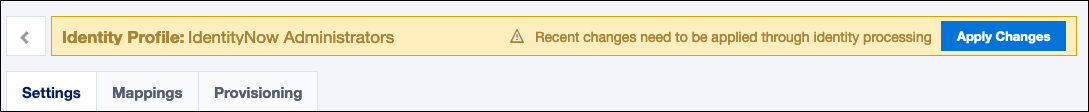
To manually start identity processing, select Apply Changes on an identity profile or on the role, access profile, or application list pages.
This performs the actions described in event-based processing for the affected identities:
- From the role, access profile, and application pages, this runs for Active and Inactive (short-term) identities.
- From the identity profile, this runs for identities associated with that profile.
Best Practice
These processes are time- and resource-intensive. For best results:
- Complete all desired role, access profile, and application changes before selecting Apply Changes to recalculate membership and access for all of those at once.
- Save and preview your identity profile changes to verify the expected results before selecting Apply Changes.
When you select Apply Changes for roles, access profiles, or applications, you can select Review recent configuration changes before you initiate the job. This will open a pre-defined search showing changes made since manual identity processing was last initiated for all identities through the role, access profile, and application pages. This can help you anticipate the impact of the identity processing job you are initiating.
Manually Processing for Select Identities
You can also initiate identity processing for a set of identities.
- Go to Admin > Identity Management > Identities and find the identity you want to process.
- Select Actions
 > Process Identity.
> Process Identity.
This performs the actions described in event-based processing for the affected identity.
To process multiple identities, select the checkboxes next to the identities you want to process, select the Actions menu, and choose Process Identities.
Monitoring Identity Processing
When identity processing is executing, you can go to Admin > Dashboard > Monitor to monitor the running process in the Active Jobs list.
You can also use Search to review audit records of identity processing jobs initiated with Apply Changes. Use this query to see the start and end records for each execution: name:"Manual Identity Processing Started" OR name:"Manual Identity Processing Passed".
Synchronizing Identity Data After Processing
When an identity changes after processing, its data is synchronized across connected services like Search and other systems. Identities are typically synchronized at the same time they are updated. However, in some cases, identities are not processed yet have data changes that affect associated identity data. To capture these cases, the SYNCHRONIZE_IDENTITIES job runs daily at 1:00 AM CST/CDT (6:00 AM UTC) in every tenant. This reconciliation job scans eligible identities in the tenant, determines which changes are necessary, and synchronizes them as needed.
Note
Identities in the Inactive (long-term) identity state are excluded from the SYNCHRONIZE_IDENTITIES job to reduce the system resource consumption and ensure other nightly scheduled jobs are completed.
The job’s speed depends on system load and other identity-related operations. For example, provisioning processes and aggregations may lock identities to maintain their state. For these cases, synchronization will occur after these locks are released.
Note
Submit a Support ticket to adjust the time that the SYNCHRONIZE_IDENTITIES job is scheduled to run.
Confirming Identity Update Status
Identity data shows when each user was last updated in Identity Security Cloud.
- Go to Admin > Identity Management > Identities.
- Find and select an identity.
- In the Details tab, view the Modified date to determine when the identity was updated.
Documentation Feedback
Feedback is provided as an informational resource only and does not form part of SailPoint’s official product documentation. SailPoint does not warrant or make any guarantees about the feedback (including without limitation as to its accuracy, relevance, or reliability). All feedback is subject to the terms set forth at https://developer.sailpoint.com/discuss/tos.