Viewing Permissions
The Permission tab provides four different views on a resource:
-
Simple - High level view that shows who has direct access to what. You can filter the results by the permissions type (menu on the left panel).
If a permission is directly granted, you can revoke a user's permission from this view. Select the more options button within the Actions column on the user you want to revoke and select Revoke. A dialog appears confirming if you want to continue with the revocation.
Another option within the Actions column is View Paths. This path shows how the user was given the permission and also has the revoke function available. Once viewing a permission path, permissions can be revoked here by hovering over the permission and selecting the blue revoke button. This button is not displayed for all permissions, only revocable ones.
-
Tree - Gives the view from a resource perspective on the entire resource.
If a permission is directly granted, you can revoke a user's permission from this view. If you hover over a permission and a blue revoke button displays, that permission can be revoked. Select Yes to start the revocation task.
Note
Revoking permission is only supported for OneDrive and SharePoint Online.
What Permission can be Revoked?
A user permission directly granted which are not inherited qualifies to be revoked.
| Where is Permission Granted From? | Can it be Revoked? | Notes |
|---|---|---|
| User direct access on resource | Yes | The primary creator/owner or high-level admin of the resource cannot be revoked even if directly granted. See table below. |
| Permission inherited from parent | No | |
| Permission inherited from group | No |
Note
When a user is granted Full Control to a resource in OneDrive or SharePoint Online, the OneDrive or SharePoint Online modern view will recognize that as Owner. When an Owner permission is assigned in this manner, it can be revoked by permission revocation in Data Access Security.
In the case that a single user is granted both Owner via the Site Collection Administrators setting and directly on a resource, Data Access Security will treat these as a single permission prioritizing the permission inherited from the Site Collection Administrators. Therefore, in the Permissions view, only one instance of Owner permission will appear for this user. Since the permission is inherited, the Revoke option will not be available.
Note
Within OneDrive and SharePoint Online, a user can have the same access by having direct access and a corresponding shared link. If permission is revoked, only the targeted permission (either direct access or from the shared link) will be removed, the other will be unaffected.
Revocation Audit Events
Revocation tasks create various events which can be audited using Identity Security Cloud Search. These events can be viewed in Search using the following queries:
- type:PERMISSION_REVOKED
- operation:REVOKE_PERMISSION
Revocation Special Use Cases
| Microsoft Modern View Permission Name | Microsoft Advanced View Permission Name | Where is Permission Granted From? | Can it be Revoked? | Notes |
| Owner | Full Control | User Direct Access | Yes | OneDrive and SharePoint Online UI labels these as Owner, but they are standard direct permissions. |
| Permission Inherited from Parent | No | |||
| Permission Inherited from Group | No | |||
| Owner | Site Collection Administrators Setting | No | The primary creator or owner of the resource cannot be revoked. | |
| Site collection administrator | User Direct Access | No | High-level admin rights cannot be revoked. |
-
Overexposed - Accessible by everyone or a larger part of the organization. The definition for overexposed can be configured through the Overexposed Resources section within the General tab under Settings. There are three different scope or view types:
- Unique Permissions or Critical Data
- Unique Permission only
- Critical Data only
-
Excess — View users who overlap and have redundant access paths granting similar or excessive permissions to the same resource.
Overexposed View
This screen allows the user to view overexposed resources which are resources that have numerous members.
You can view the following information on this screen:
- The resource path of the selected resource
- The group responsible for the overexposure
- The type of overexposed access
- The data classification categories within the resource
All connected applications display within the left-hand window under the All Application tab. If there are a lot of applications, there are multiple ways to find the desired one.
If you know the application name or application path, use the search bar to locate it.
Use the filter icon in the search bar to select the Search contains resource name option. This option allows the user to fine-tune the search if they know a specific name or phrase in the name of the application.
Under the My Resources tab, a user can see all of the resources they own.
Note
Administrators can view both the All Application and My Resources tabs. Data owners can only view the My Resources tab.
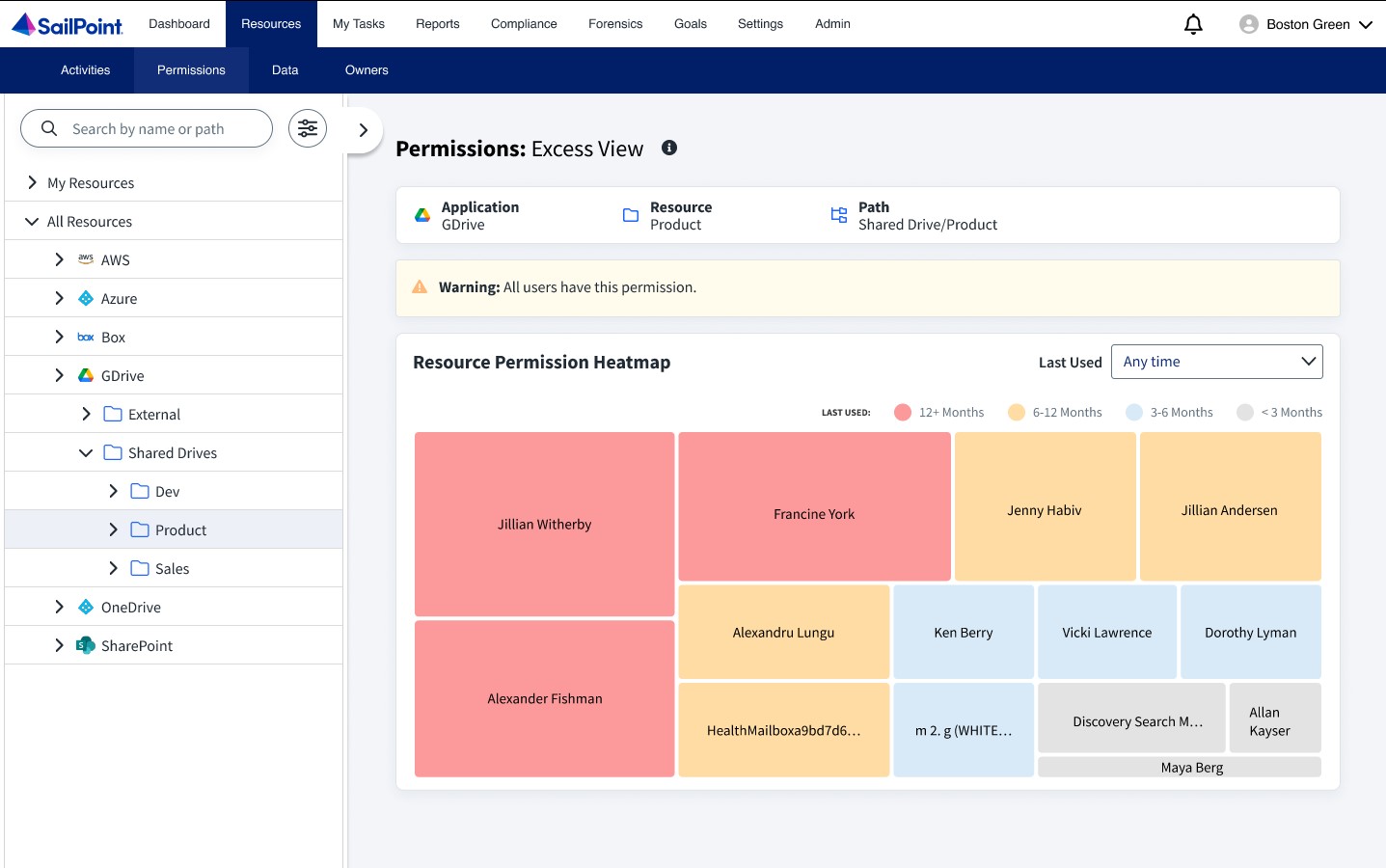
Excess View
This screen provides information on users who have excessive permissions within the organization, such as stale or redundant permissions. The heatmap visually displays these excess access paths for the selected resource.
The size of each block represents the amount of redundant access paths that have been granted or the amount of excessive permissions that the resource has. The heatmap blocks have distinct colors according to the time period they have been unused by the user. The color legend which depicts the level of staleness is at the top of the heatmap.
Additionally, the Excess View screen allows data to be filtered based on permission staleness.
Selecting a block provides the user with a snapsnot of information regarding that resource including user information, the permission count, and the types of permissions granted. For more information on that selected resource, select View Access Paths.
After selecting View Access Paths, you can select between two tabs on the View Details window.
- Permission List – provides the same type of info that was presented when the resource block was selected from the heatmap.
- Access Paths – provides a tree view of the user with all of the access they have. Each colored branch depicts the timeframe that resource was last used.
Documentation Feedback
Feedback is provided as an informational resource only and does not form part of SailPoint’s official product documentation. SailPoint does not warrant or make any guarantees about the feedback (including without limitation as to its accuracy, relevance, or reliability). All feedback is subject to the terms set forth at https://developer.sailpoint.com/discuss/tos.