Working with Certifications
Your administrator may create a certification campaign containing access items or identities you're responsible for. When this happens, you'll receive an email and in-app notification that certifications are ready for your review. You may continue to receive reminder notifications about the certification until you complete your review.
Reviewing Certifications
Note
Certification reviews are disabled on phones and tablets. For more information, refer to Supported browsers and operating systems.
-
Select Certifications from the navigation menu.
-
In the Active tab, select the certification you want to work on.
-
Review the contents of the certification. The page will differ based on the type of certification:
-
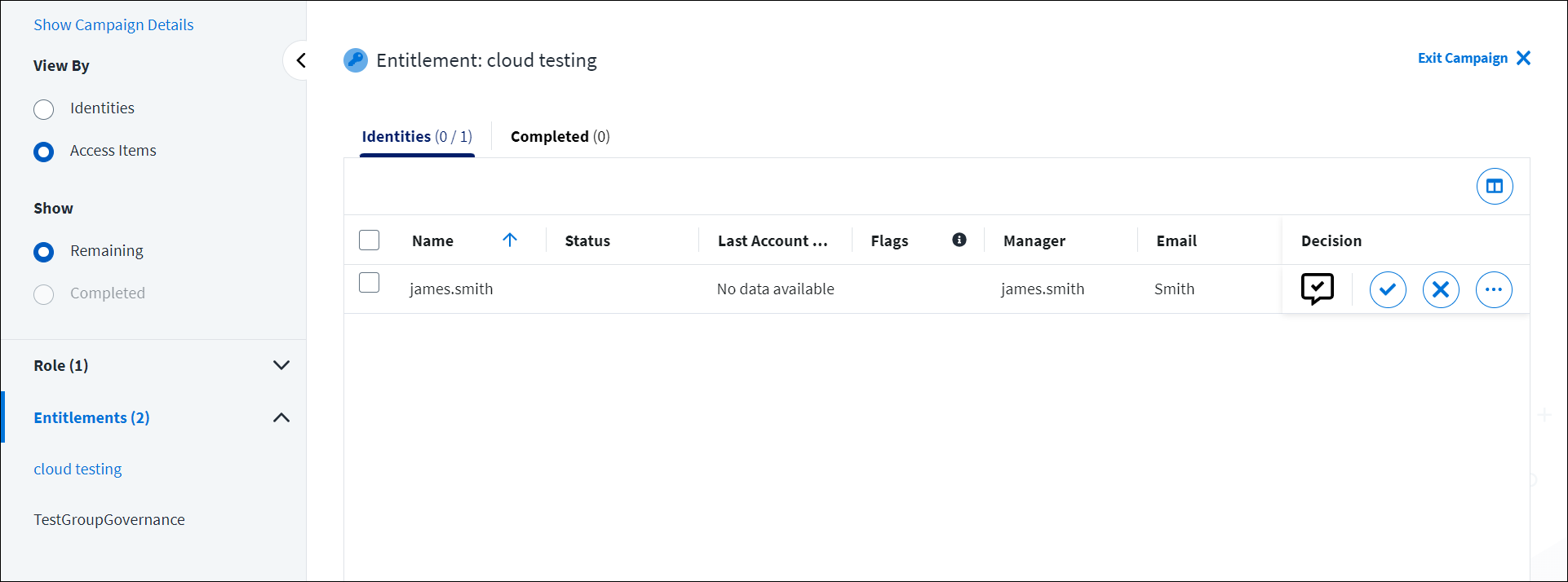
Identity access certifications
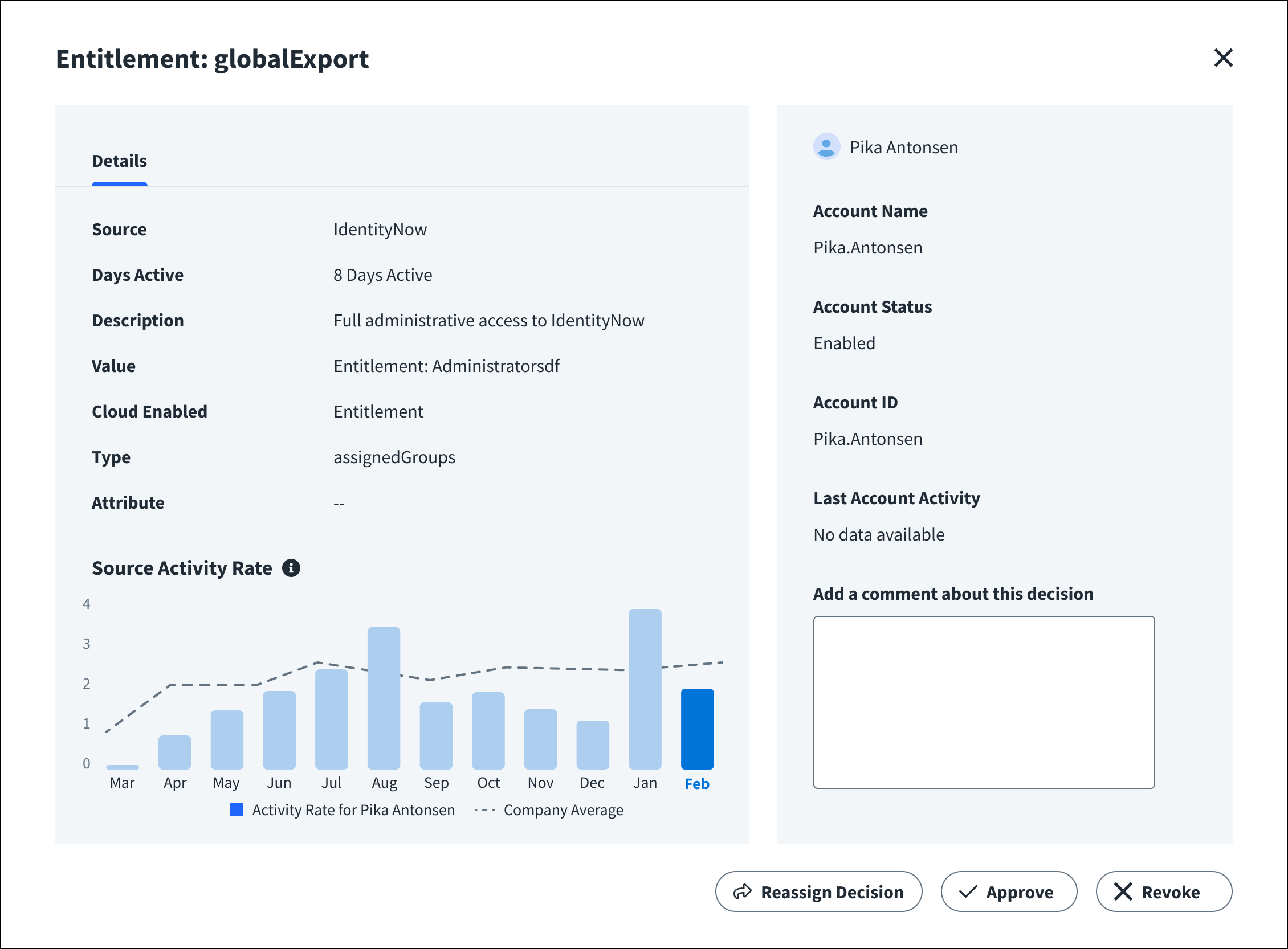
Select Identities and choose an identity from the list. You'll see a list of access items for that user. Review their access within the Roles, Access Profiles, or Entitlements tabs. Select an access item to view its details.
You can also select Access Items and choose a role, access profile, or entitlement from the list. Review the identities who have that access.
-
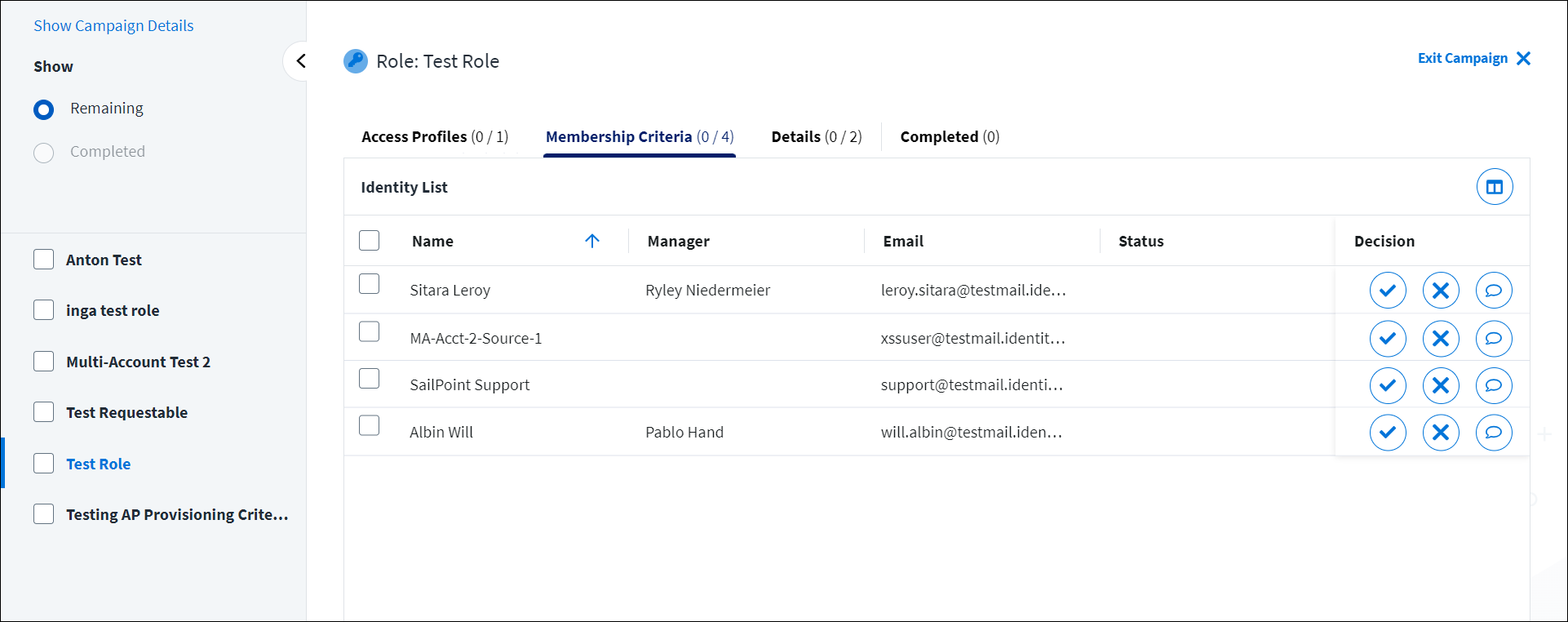
Role composition certifications
Select the role you want to review from the list of roles. Review the role's associated access profiles, membership criteria, and details.
-
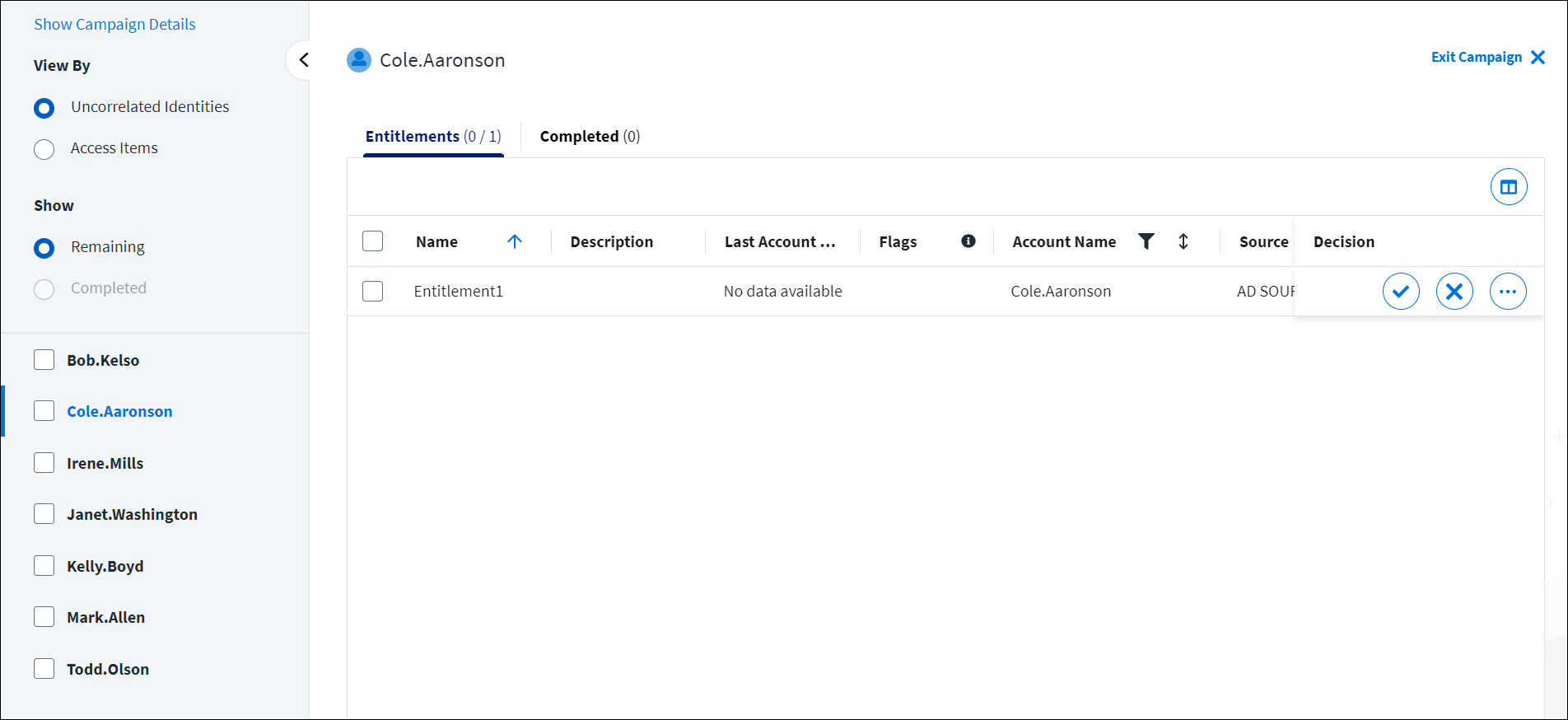
Uncorrelated accounts certifications
An uncorrelated account is a source account that is not matched to an authoritative identity. A single uncorrelated account is generally represented by an uncorrelated identity. In rare cases, multiple uncorrelated accounts may belong to the same uncorrelated identity and be grouped together.
To review these certifications, select Uncorrelated Identities and choose the uncorrelated identity you want to certify from the list. Review the access items associated with the uncorrelated identity.
You can also select Access Items and choose an access item from the list. Review the uncorrelated accounts associated with that access item.
-
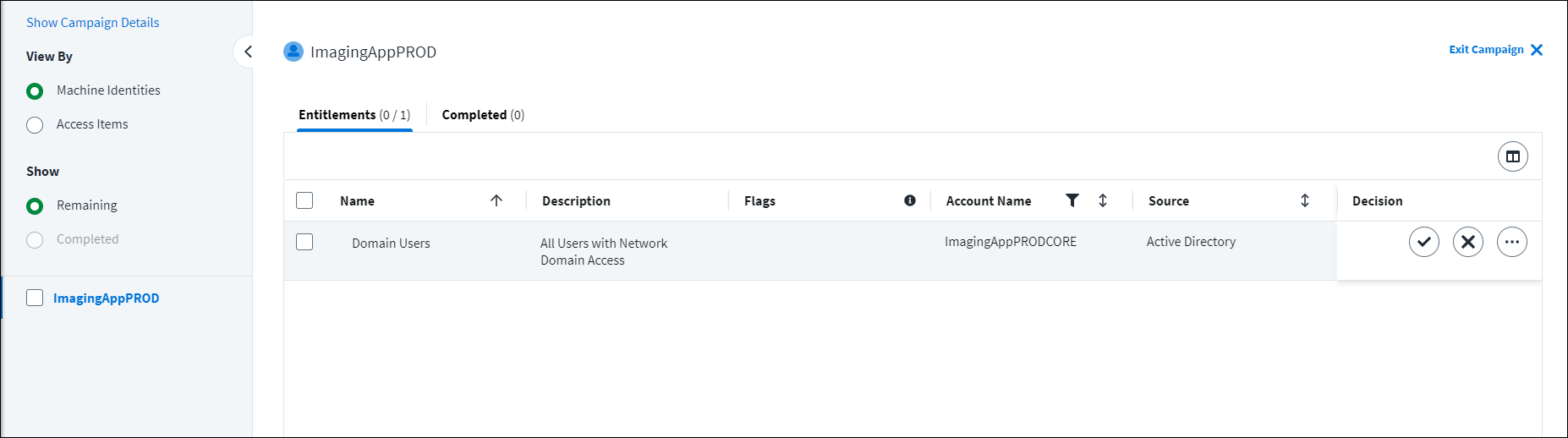
Machine accounts certifications
A machine identity is a representation of a business application or process that machine accounts, like service accounts, bots, or other types of non-human accounts, are grouped within. For example, Automated Teller service accounts may be grouped and correlated to a Automated Teller machine identity.
To review these certifications, select Machine Identities and choose an identity from the list. You'll see a list of access items for that machine identity. Review their access within the Entitlements tab. Select an access item to view its details.
You can also select Access Items and choose an entitlement from the list. Review the machine identities that have that access.
-
-
In each section, beside each item, select Approve icon
to approve access or Revoke
to revoke access.
Notes
- Roles that were automatically assigned to identities through membership criteria may only be acknowledged. In these cases, select Acknowledge to review this access.
- If you revoke an access profile that contains an entitlement that is also assigned to a user through another access profile, all entitlements within the access profile will be revoked, except for the common entitlement.
Some reviews may require that you include a comment explaining your decision. For example, if you choose to revoke an item in a role composition certification, you must enter a comment that explains why and how the role should be changed. The system will send a task with these comments to the role owner to update the associated role. Select Submit to submit your comment and complete your review for this access.
While completing your review, you can reassign the certification if you feel there is a user who is better suited to review this access.
Tips for reviewing certifications
- Your certifications may contain access flags and additional data from other SailPoint products and services your organization has licensed. This information can help you make more informed decisions about whether to approve or revoke each access item.
- If configured by your administrator, you can also view additional attributes for entitlements to help make decisions on access. To do so, select an entitlement and view the Additional Attributes section within its details. You can also select individual entitlements within an access profile to view their additional attributes.
Select More Options
to leave comments with your decision, reassign the certification, or choose a revocation date. In the new window, enter the revocation date or comments about the certification and submit your decision.
Note
You cannot set a revocation date for entitlements.
You can change your decision, add or modify a revocation date, or add additional comments until you sign off on the certification. In the Completed tab of an identity or access item, select Revisit Decision
for the decision you want to update. After you complete a certification, you can add or modify a revocation date, add additional comments, or change your decision by selecting More Options
.
You can save and return to your work at any time by selecting Exit Campaign in the upper-right corner of the page.
After you've reviewed each item, you can submit your decisions and complete the certification.
Access Flags
When you review an access item for a certification, an icon may display in the Flags column. This icon alerts you of information you should consider when approving access. You may encounter the following flags:
| Name | Icon | Definition |
|---|---|---|
| New Access |  |
The access has not been certified previously. |
| Birthright Access |  |
The access has been granted by automated rules, such as lifecycle states. |
| High Privilege (Overridden) |  |
The entitlement's privilege level has been manually changed to indicate it grants access to sensitive data with high security risks. |
| Contains Privileged Access |  |
The access profile or role contains an access item with privileged entitlements. Privileged entitlements may grant access to sensitive data with high security risks. |
| Timebound Access |  |
The access has a set end date. |
| Comments |  |
There are comments associated with this access. |
| Cloud Enabled |  |
This access relates to cloud infrastructure. |
| Critical Data Access |  |
This access contains critical data. |
Viewing Critical Data
If your organization has SailPoint Data Access Security, you can view the impact score, policies, and data categories for entitlements.
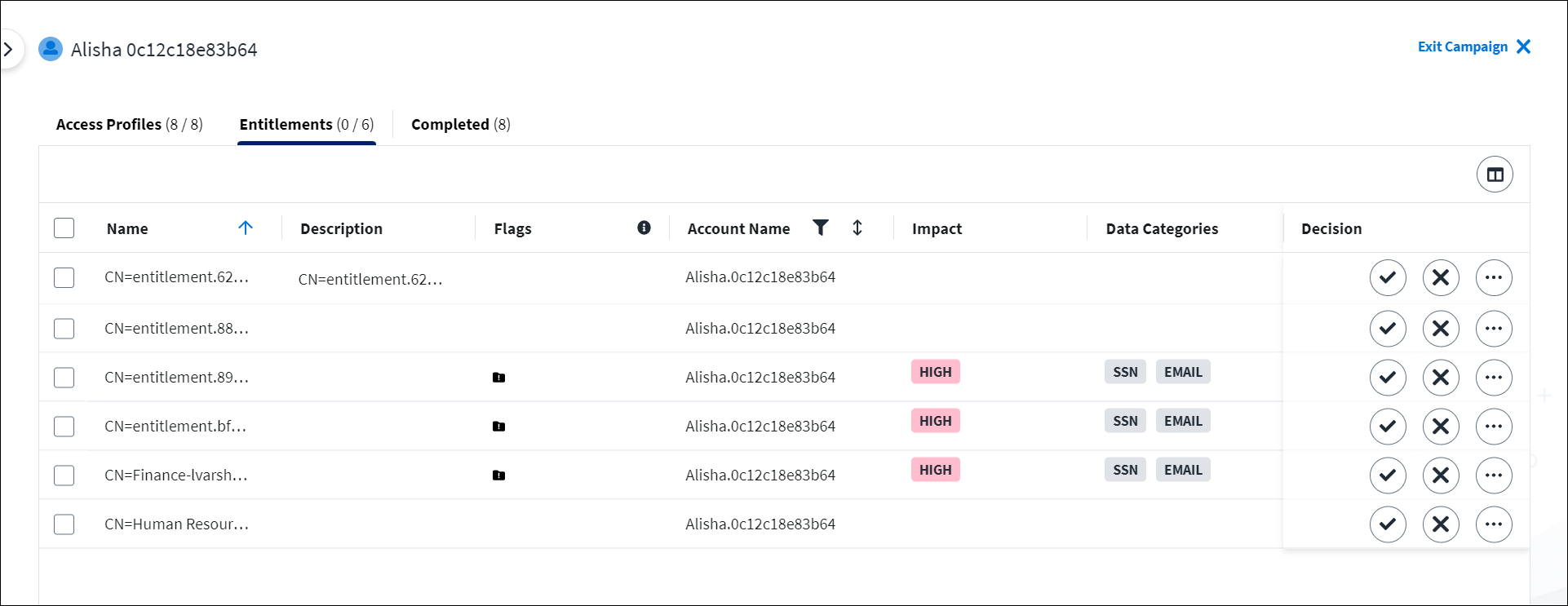
The Impact Score is calculated by combining the perceived sensitivity of the data it grants access to with the number of instances of that data type. For example, an entitlement that grants access to 1000 social security numbers will have a higher Impact Score than an entitlement that grants access to 20 email addresses. The Impact Score can be High, Medium, or Low.
The Policies columns lists the policies associated with the data.
The tags within the Data Categories column describe the types of critical data the user will maintain access to if their access is approved.
Viewing Last Account Activity
If your organization has SailPoint SaaS Management, you can review the Last Account Activity column for each access item to determine when the user last accessed the account associated with the access.
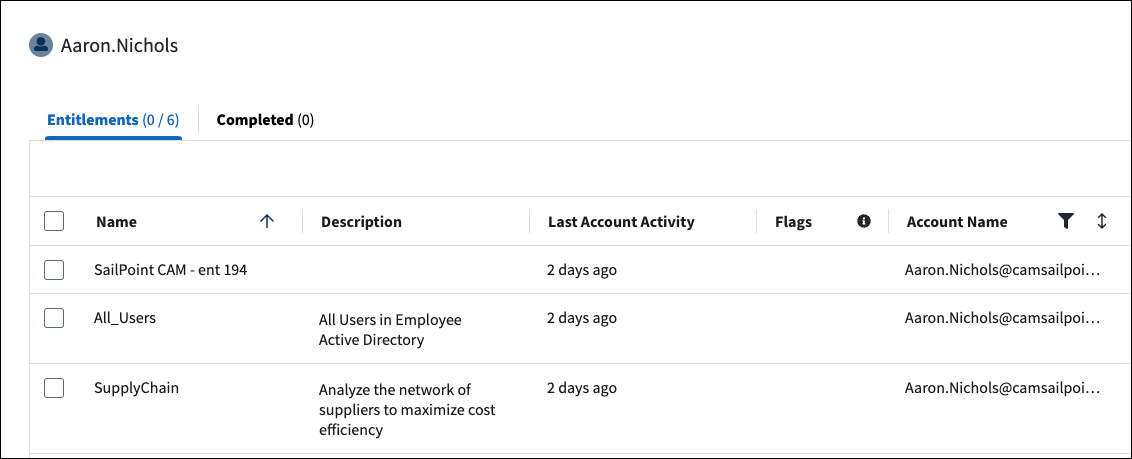
This data describes when a user last accessed the account with that access profile or entitlement. The data does not describe when the access profile or entitlement was last used.
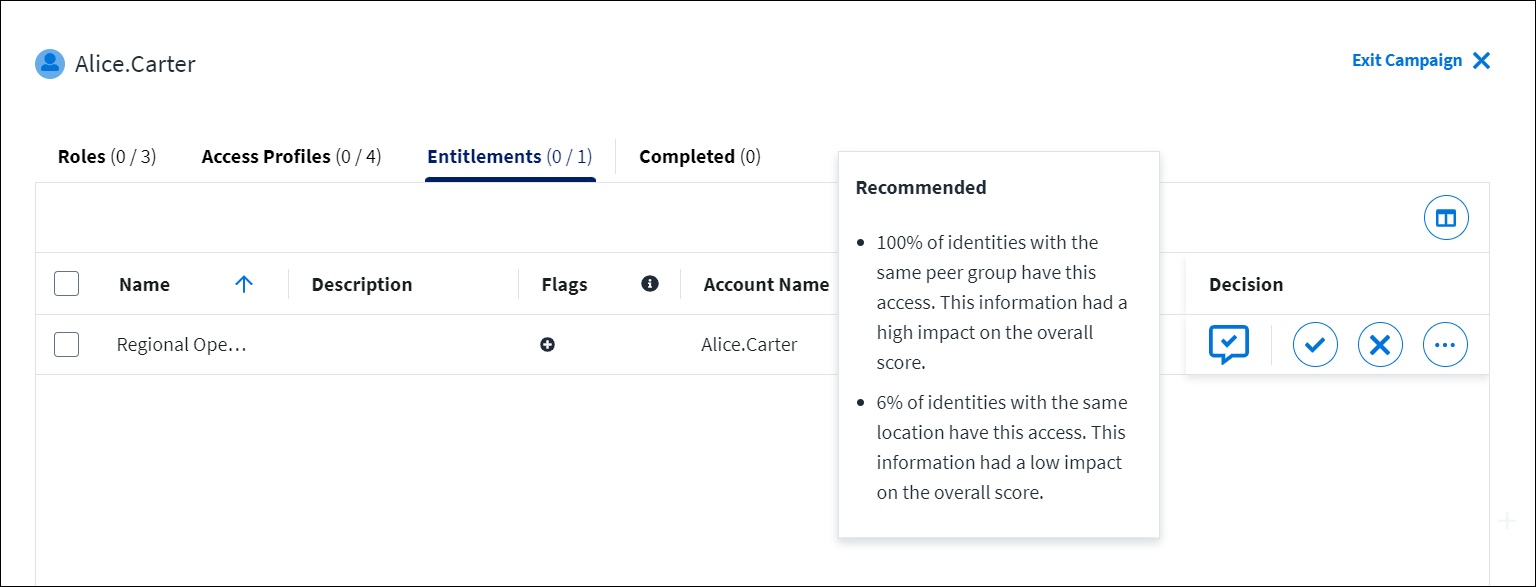
Viewing Recommendations
If your organization has the Recommendations service, select the Recommended 

Viewing Source Activity
If your organization has Activity Insights, you can view the Days Active column to determine how many days the identity was active on the source for the past 90 days.
You can use this information to determine how often the identity used the source and if they should still retain access to the entitlement.
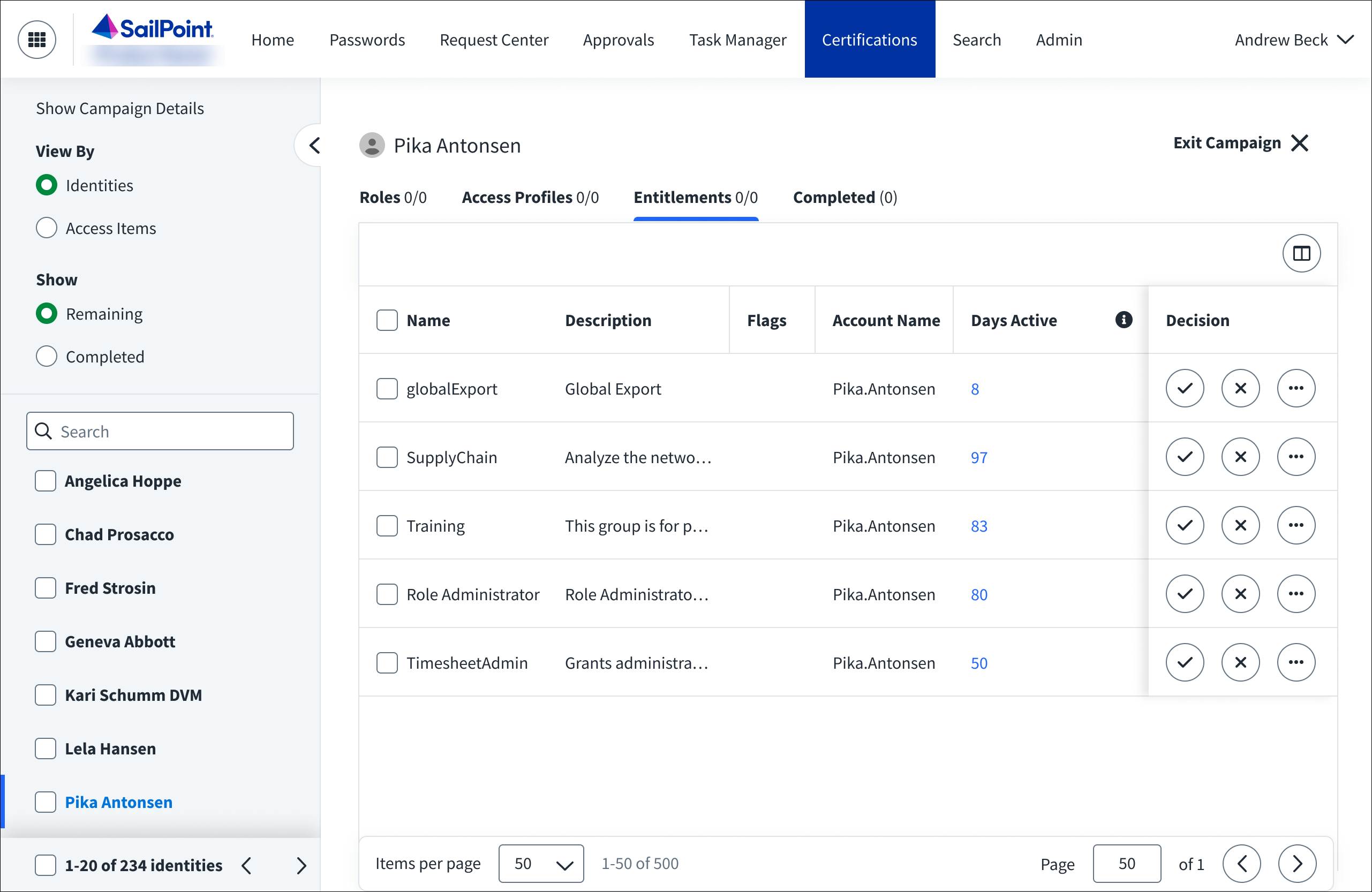
Selecting the number of days opens a chart that displays the identity’s source activity for the past year and compares their activity to the company’s average.
Completing Certifications
After you've reviewed each item, you'll be taken to a sign-off page to complete your certification.
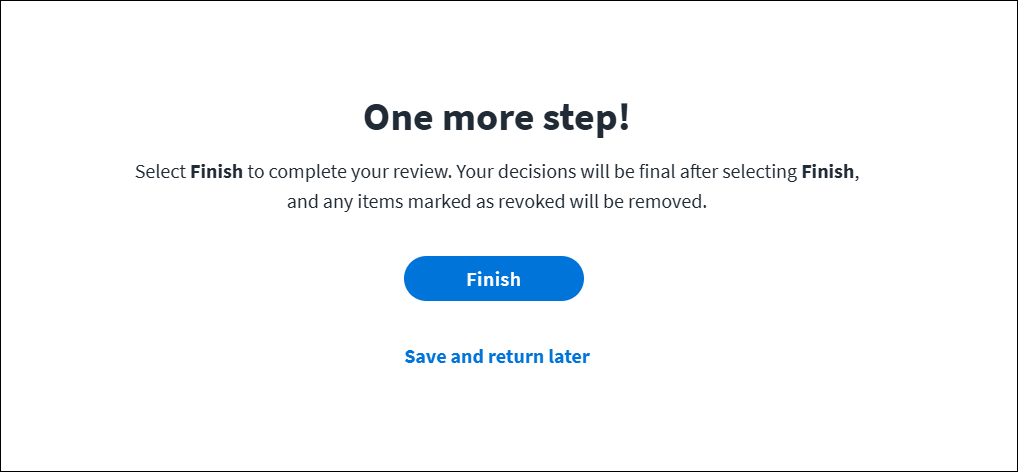
To complete your review, select Finish. The certification moves to the Completed tab.
Important
Before you complete your review, ensure your decisions are correct and final. You will not be able to make any changes after you've submitted your decisions, and any access marked as revoked will be removed.
If you are not ready to submit your decisions, you can save and return later by selecting Save and return later.
Documentation Feedback
Feedback is provided as an informational resource only and does not form part of SailPoint’s official product documentation. SailPoint does not warrant or make any guarantees about the feedback (including without limitation as to its accuracy, relevance, or reliability). All feedback is subject to the terms set forth at https://developer.sailpoint.com/discuss/tos.