Working with Networks
Cloud Access Management shows cloud resources that include data unique to networking such as subnets, security groups, and virtual private clouds (VPCs). Virtual machines or instances are also displayed due to their affinity with other network resources.
Viewing a Summary of Networks
You can view details for the following network types:
- Virtual Private Clouds
- Subnets
- Route Tables
- Security Groups
- Instances
Select Networks in the left navigation menu to view an overview of the networks that Cloud Access Management has discovered across your cloud sources.
Select a tab at the top to switch views. For example, to view the Security Groups, select the Security Groups tab to see the name, source, region, object type, subnets, instances, VPC, and tags associated with each group.
You can search within the overview list using the search bar below the tabs. Select the download icon
![]() to generate and download a CSV with the information for your selected tab.
to generate and download a CSV with the information for your selected tab.
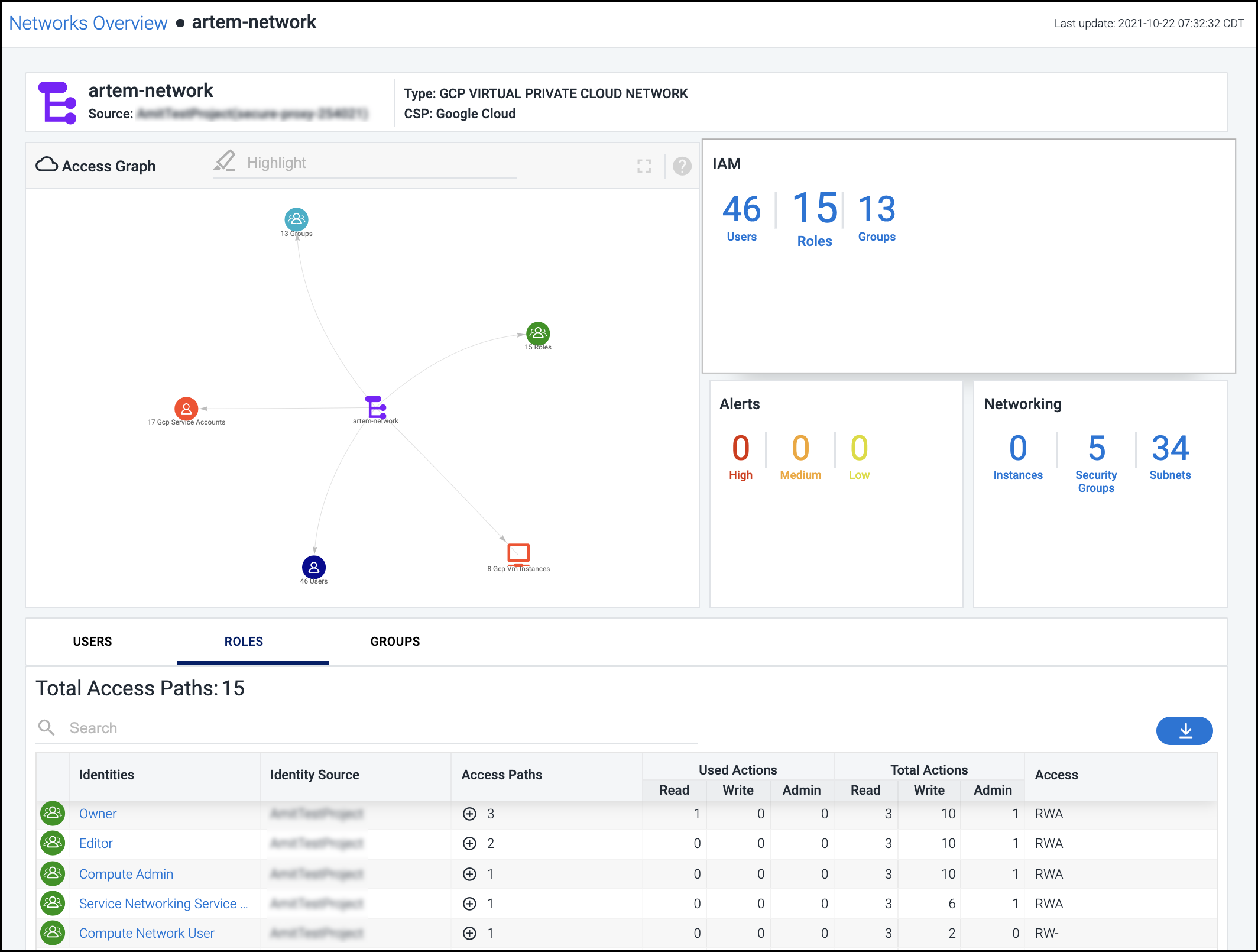
Viewing Access Details for a Network
Select a network object from the overview list to see a summary of the total access paths affecting the network.
Select a tile to display more detailed information about it in the list below. The access graph is also updated based on your selection. For information on using the access graph, see Using the Access Graph to Understand Relationships.
Select the numbers on a tile to display more information about the selected type in the Total Access Paths list below.
IAM - Shows the number of users, roles, and groups within that identity access management network.
Alerts - Shows the number of violations discovered for this network based on severity. Select this tile for a detailed view into these alerts. For more information, see Viewing and Triaging Alerts.
Networking - Shows different numbers based on the network type.
| Network Type | Networking Objects Shown |
|---|---|
| VPCs | Instances, security groups, and subnets |
| Subnets | Instances and security groups |
| Route Tables | Instances, subnets, and routes |
| Security Groups | Instances and firewall rules |
Objects - (Instances only) Shows the number of total and used accessed objects discovered on the instance.
Role - (Instances only) Shows the number of total and used roles discovered on the instance.
Documentation Feedback
Feedback is provided as an informational resource only and does not form part of SailPoint’s official product documentation. SailPoint does not warrant or make any guarantees about the feedback (including without limitation as to its accuracy, relevance, or reliability). All feedback is subject to the terms set forth at https://developer.sailpoint.com/discuss/tos.