Configuring Identity Providers
Cloud Access Management supports connecting to identity providers (IDPs) to show effective or federated access between enterprise directory groups and cloud resources.
Linking your IDP with Cloud Access Management allows it to detect cloud access for outside users without local cloud credentials or native user access. This gives you greater visibility and context into who has cloud access and how that access is being granted.
Configuring Azure Active Directory
If you are using Microsoft Azure Active Directory (AD) as your enterprise directory, you can configure Azure as your identity provider to provide federated access to Amazon Web Services (AWS).
Confirm the following is configured in your Azure and AWS cloud environments before proceeding:
- Refer to the Microsoft tutorial on integrating Azure Active Directory single sign-on (SSO) with Amazon Web Services (AWS).
- In the Azure portal, confirm the groups you are using to map access to AWS are entered correctly. You can look up the application under Enterprise Applications on the Azure portal.
-
Copy the Application ID corresponding to the AWS application in the Overview page.
Configuring Okta
In order to register Okta to work with Cloud Access Management, you will need to connect Okta to AWS. Refer to the Okta help for guidance.
In order to register your Okta source with Cloud Access Management, you'll need to find the application ID. After you've configured the AWS Account Federation app in Okta, you can choose to have multiple instances of the app with different names. Identify the name of the specific instance you want to onboard with Cloud Access Management before proceeding.
-
Log into Okta and go to the admin portal.
-
Select Applications.
-
Search for the name of the AWS instance you want to onboard and select it.
-
Once you have selected the application, copy the application ID embedded in the URL.
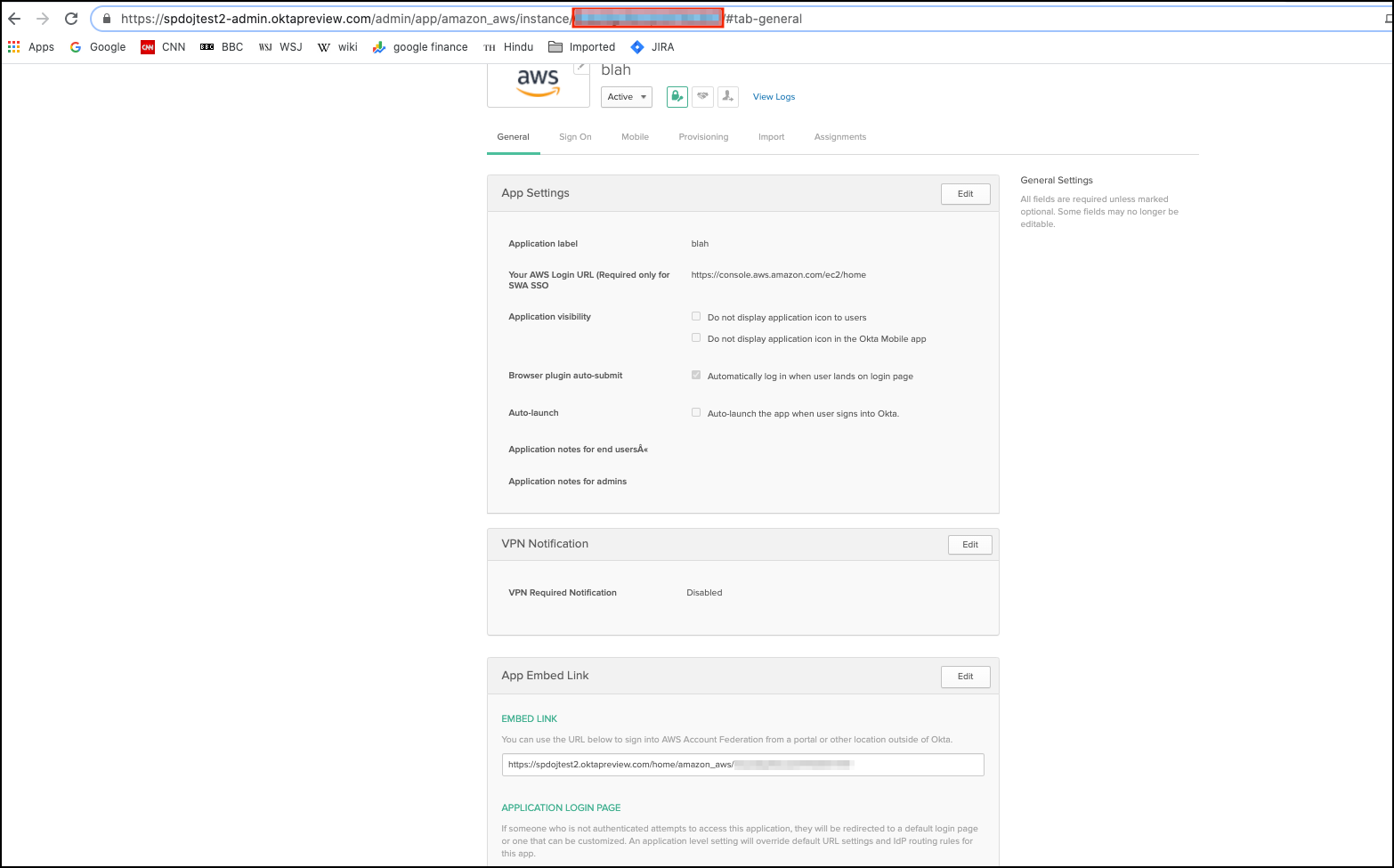 5. Paste the application ID when you register Okta.
5. Paste the application ID when you register Okta.
Next Steps
- Once you have configured your identity providers, you can register your IDPs.
- Registering allows Cloud Access Management to identify cloud access by roles federated with an identity provider.
Documentation Feedback
Feedback is provided as an informational resource only and does not form part of SailPoint’s official product documentation. SailPoint does not warrant or make any guarantees about the feedback (including without limitation as to its accuracy, relevance, or reliability). All feedback is subject to the terms set forth at https://developer.sailpoint.com/discuss/tos.
